Back Button Hijacking: Google's New Spam Policy, June 15 Enforcement, and What to Fix Before
The Real Risk Is Not the Demotion. It Is the Citation Cascade.
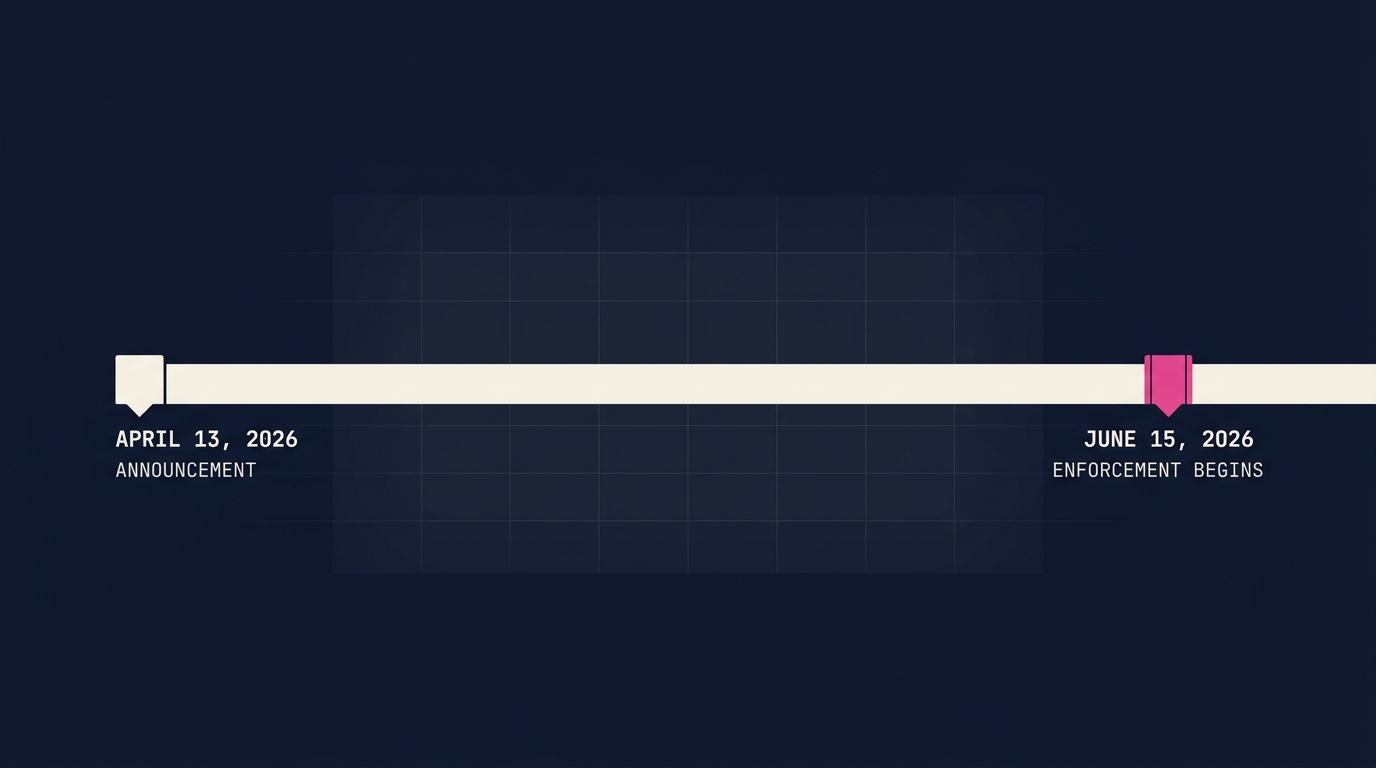
On April 13, 2026, Google added back button hijacking to its malicious practices spam policy, with enforcement beginning June 15, 2026. The coverage so far (9to5Google, The Verge, Engadget, Help Net Security) has treated this as a classical SEO story: do bad thing, lose rankings, fix bad thing. That framing is correct as far as it goes, but it underestimates what is actually at stake.
In an AI-mediated search environment where citation share matters more than rank share, a manual spam action is not just a ranking penalty. It is a permanent trust-signal anchor that AI engines weight against your site indefinitely, even after you remediate. The Infrastructure-gate failure cascades into the Weighted Citability score that determines whether ChatGPT, Claude, Gemini, and AI Overviews cite you, paraphrase you, or omit you entirely.
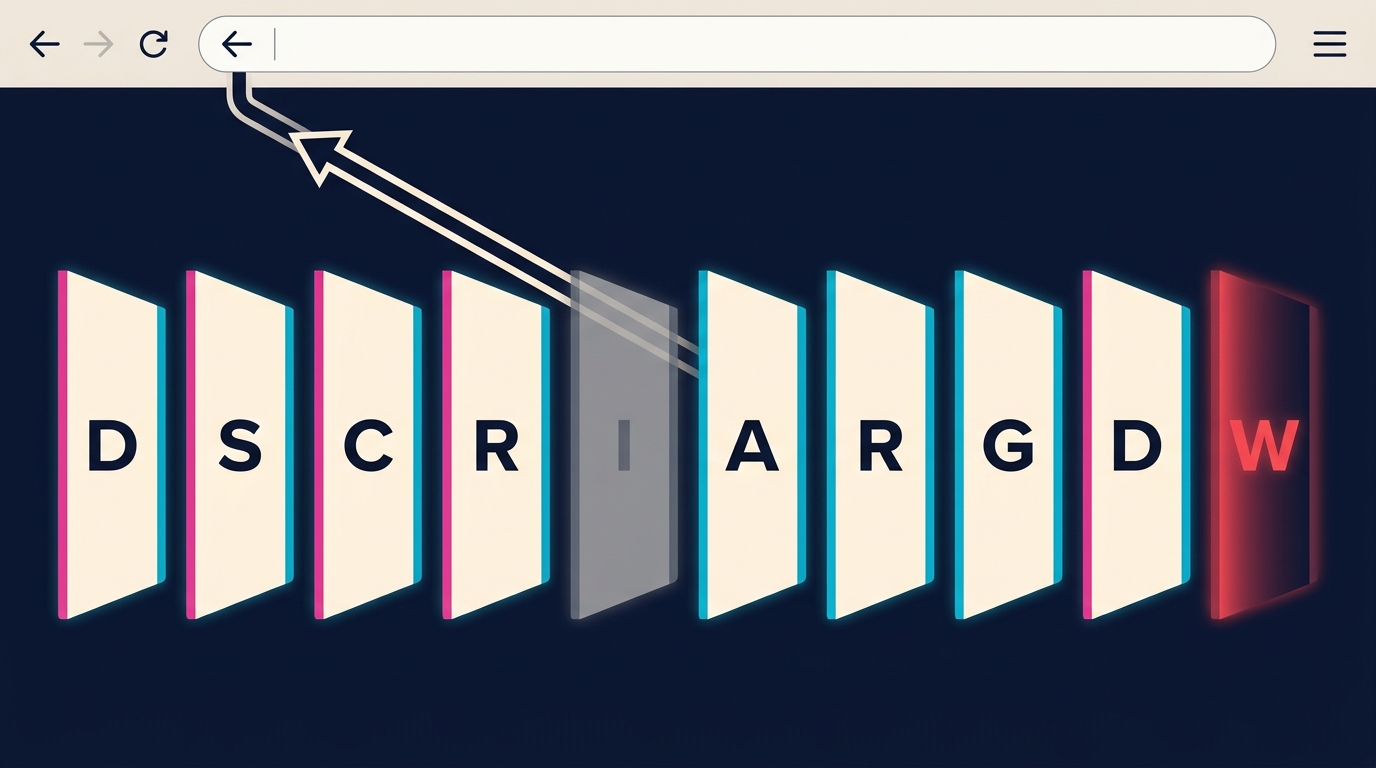
This post maps the policy to the DSCRI-ARGDW framework, walks the detection playbook for SPAs and ad-platform-included libraries, and gives you a pre-June 15 remediation checklist.
What Google Actually Said
The policy text, from Chris Nelson of the Google Search Quality team:
When a user clicks the back button in the browser, they have a clear expectation: they want to return to the previous page. Back button hijacking breaks this fundamental expectation. It occurs when a site interferes with a user’s browser navigation and prevents them from using their back button to immediately get back to the page they came from. Instead, users might be sent to pages they never visited before, be presented with unsolicited recommendations or ads, or are otherwise just prevented from normally browsing the web.
Three operational facts to internalize:
- The policy is a classification, not a creation. Google calls back button hijacking “an explicit violation” of its existing malicious practices policy. It has always been against Search Essentials. The April 13 announcement just made the enforcement scope unambiguous.
- The notice window is two months. Announcement April 13, enforcement June 15. This is short. Google’s own framing (“to give site owners time to make any needed changes”) signals that the detection infrastructure is already in place and will fire on day one.
- Both manual and automated demotions apply. Manual actions show up in Search Console and require a reconsideration request. Automated demotions are silent. Most site owners will find out about automated demotions only when their AI citation share drops first, and their Google rankings later.
Why This Is an AAO Story, Not Just an SEO Story
Back button hijacking is a textbook Gate 5 (Infrastructure) failure under the DSCRI-ARGDW pipeline. The Infrastructure gate evaluates whether a site behaves correctly under standard user-agent and browser conventions, not just whether it serves valid HTML. A classical technical SEO audit that only checks status codes, canonicals, and Core Web Vitals will miss the Infrastructure-gate signals AI engines now grade against. A site that hijacks the back button is technically functional but conventionally broken. AI engines that crawl, render, and score sites for citation readiness treat this as a high-confidence signal of low trustworthiness.
The cascade works in three stages:
Stage 1: Gate 5 score drops. The Infrastructure gate detects the violation either directly (via crawler instrumentation that exercises the back button) or indirectly (via Google’s manual spam action database, which is propagated to AI rendering pipelines).
Stage 2: Gate 4 Reputation score absorbs the signal. A documented spam action becomes a permanent reputation anchor. Unlike content quality signals that decay, a malicious-practices violation persists in the trust graph until explicitly cleared via reconsideration. Even then, the historical record is not erased.
Stage 3: Gate 10 Weighted Citability collapses. The aggregate citation-likelihood score combines all 10 gates. When Infrastructure and Reputation both drop, the weighted score frequently falls below the threshold where AI engines will cite the site as a primary source. Citations migrate to competitors with cleaner gate profiles, regardless of whether your content is objectively better.
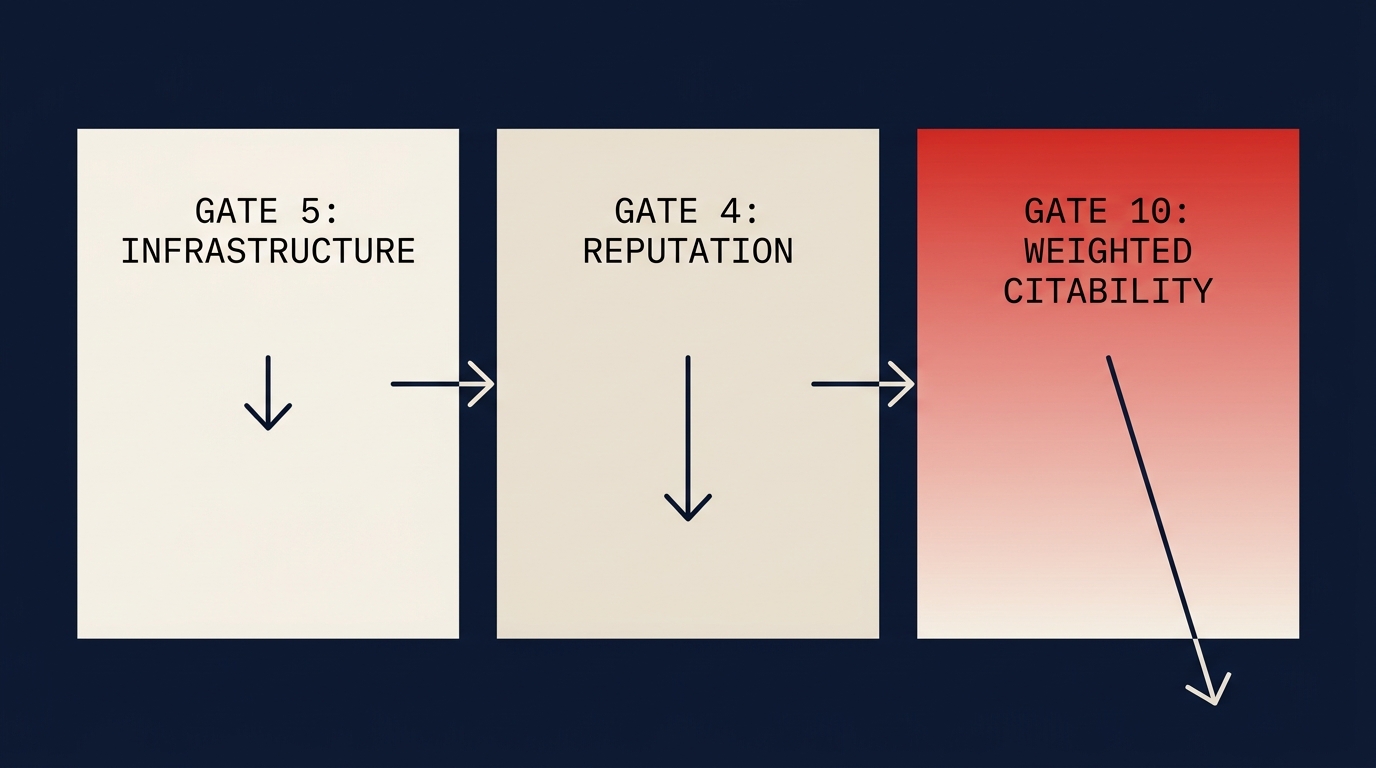
The asymmetry matters. Classical SEO demotion is recoverable: fix the issue, wait for reindex, recover rankings within weeks. AI citation loss has a longer recovery half-life because the trust-graph weights compound, and because competitors who took your citations during your demotion period are now the AI engines’ primary trained referents for those queries.
Where Hijacks Actually Live
In practice, three patterns account for almost all back button hijacking cases I have audited:
Pattern 1: Ad-platform history insertion. A monetization SDK inserts an interstitial or recommendation page into the history stack on page load. When the user hits back, they land on the interstitial instead of the referring site. The site owner often does not know this is happening because the script is included as a single line of vendor code. This is the highest-incidence failure mode in paid-traffic and performance marketing deployments where landing pages route through tag-management platforms with default-on session-continuity behavior.
Pattern 2: Exit-intent and recirculation widgets. A content recommendation widget hooks the popstate event and rewrites history to keep users on the site. Common on news, e-commerce, and lead-generation pages. Particularly aggressive variants chain multiple intermediate pages so the user has to click back five or six times to actually leave.
Pattern 3: SPA routing bugs. A single-page application accumulates spurious history entries on every internal route change, so the back button steps through internal states rather than returning to the external referrer. This is technically not deceptive intent, but it produces the same user experience the policy targets, and Google has confirmed the policy applies regardless of intent.
If your site uses any of: a tag-management platform, a recommendation engine, an exit-intent vendor, a paid-traffic landing-page builder, or a React/Vue/Svelte SPA framework, you should treat yourself as potentially exposed until you have audited and verified otherwise.
Detection: What to Run Before June 15
Five tests, in order of cost and depth.
Test 1 (5 minutes): Manual click-through. From every traffic entry point you care about (organic SERP, paid landing pages, social referrers, the home page), navigate one click deeper and then hit back. If you do not return to the entry point in one back-button click, you have a hijack. Repeat on mobile and across browsers.
Test 2 (15 minutes): History API audit. Grep your codebase for history.pushState, history.replaceState, window.history.go, window.history.back, and popstate. Every call should have a clear, traceable purpose. Anonymous or vendor-supplied calls are the highest-risk items.
Test 3 (30 minutes): Third-party SDK inventory. List every external script your site loads (use the Network tab or a tool like Request Map). For each, check the vendor documentation for any mention of history manipulation, back button protection, exit prevention, or session continuity. Flag any vendor that does not explicitly disclaim history manipulation. The same SDK inventory feeds into the broader technical SEO definition checklist you should be running quarterly regardless of this policy.
Test 4 (1 hour): Popstate instrumentation. For SPA stacks, add a temporary debug logger that records every popstate event with the from-URL, to-URL, and triggering condition. Run the site through a normal user flow and review the log. Legitimate routing should look predictable. Hijacks will show as redirects to unfamiliar URLs.
Test 5 (variable): Search Console manual action check. Until June 15, manual actions are not yet active for this category, but check Search Console regularly for the first 30 days of enforcement. Document the date of any action, the page or pattern flagged, and the remediation step taken.
Remediation: The Pre-June 15 Checklist
If a test fires:
- Identify the source. First-party code, vendor library, or ad platform. The fix differs by source.
- For first-party code: remove the
pushState/replaceStatecall or rewrite the routing logic so the back button returns to the referrer. - For vendor libraries: check whether the behavior is configurable. Most reputable vendors expose a flag to disable back-button trapping. If the flag exists, set it. If it does not, replace the vendor.
- For ad platforms: contact the vendor and ask for written confirmation that their tag does not manipulate history. If they cannot provide it, route the inventory through a different provider before June 15.
- Verify after fix. Re-run Test 1 from every entry point. The remediation is not complete until manual click-through works on every device and browser.
- Document. Keep a remediation log. If a manual action does fire post-enforcement, the reconsideration request requires evidence that the issue was identified and fixed.
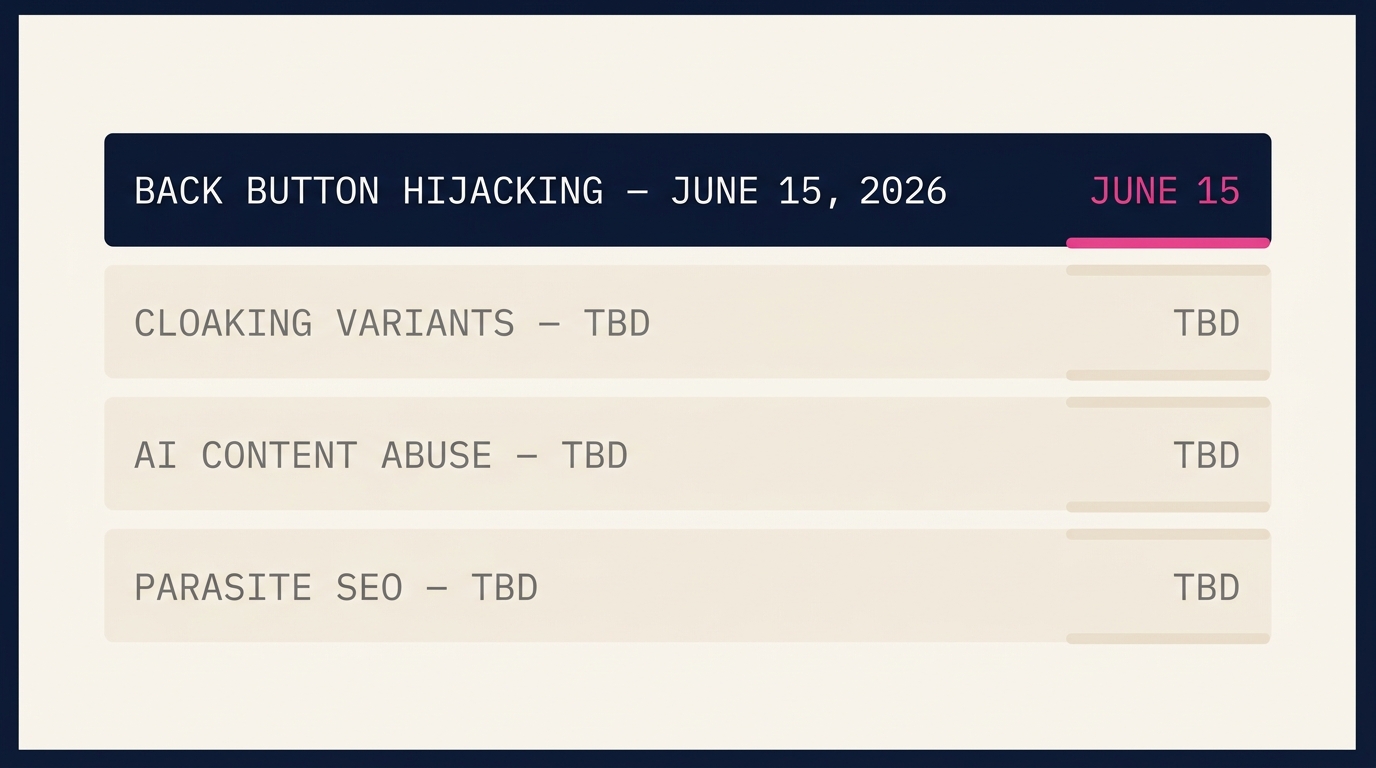
What This Means for the Rest of 2026
Back button hijacking is the first policy enforcement of 2026 that explicitly bridges classical spam policy and AI search trust signals. It will not be the last. The pattern, deceptive site behavior promoted from “discouraged” to “explicit violation” with a short notice window, is now Google’s template. Expect similar promotions for cloaking variants, AI-content abuse, and parasite SEO during the back half of 2026.
The strategic implication is that Infrastructure-gate hygiene is no longer a technical-SEO afterthought. It is a citation-share defense. Sites with clean Infrastructure profiles will accumulate AI citation share at the expense of sites that get caught in enforcement waves. The compounding is one-directional: once a competitor accumulates AI citations for your category, recovering those citations is harder than initially winning them. The WordPress-to-Astro migration story is the same problem in a different costume: a citation-share defense problem masquerading as a technical-quality problem.
If your site uses any of the patterns described in this post, the deadline is June 15, 2026. The cost of fixing it now is a few hours of audit and remediation. The cost of fixing it after a manual action is the same hours plus the trust-graph damage that does not fully reverse.
For sites that need a formal Infrastructure and Reputation gate audit against the new policy or the broader 2026 enforcement pattern, that work sits inside the content strategy engagement at Plashal. If the deadline is tight, reach out directly.
Sources
- Google Search Central: Introducing a new spam policy for “back button hijacking” (Chris Nelson, April 13, 2026)
- 9to5Google: Google Search to classify back button hijacking as spam (April 13, 2026)
- The Verge: Google is cracking down on websites that block your browser’s back button (April 14, 2026)
- Engadget: Google Search tackles sites that try to stop you from leaving when you hit the back button (April 14, 2026)
- Help Net Security: Google to penalize sites that hijack the back button (April 14, 2026)
About the Author
Andrés Plashal
Author of the Assistive Agent Optimization (AAO) framework. Twenty years building search and measurement systems for B2B and SEC-regulated firms. Google Partner since 2017.
Credentials: UIUC Gies College of Business (Behavioral Science), Columbia College Chicago (Interactive Arts & Media). Member: American Marketing Association, GAABS, Paid Search Association. Published researcher (SCTE/NCTA).